91
Tutorials and FAQs / FTP Proxy Howto
« on: November 02, 2016, 05:25:02 pm »
Allow FTP Traffic
This how-to describes the steps to allow FTP traffic from your local network to the internet and from the internet to a FTP server protected by your OPNsense firewall.
Prerequisites
To allow FTP traffic we have to redirect all FTP connections to a local FTP proxy server which dynamically inserts and removes firewall rules according to the FTP port commands.
Additionally we need rules to allow traffic on the local interface to this proxy.
For the setup of the proxy we use the "Ftp Proxy" plugin. It was released with OPNsense 16.7.8.
Forward FTP Proxy
The forward proxy enables internal clients to connect to FTP servers on the internet.

To add a new FTP proxy server navigate to Services->FTP Proxy and click on the Add Button bottom right.
Now you see a dialog with the proxy settings.
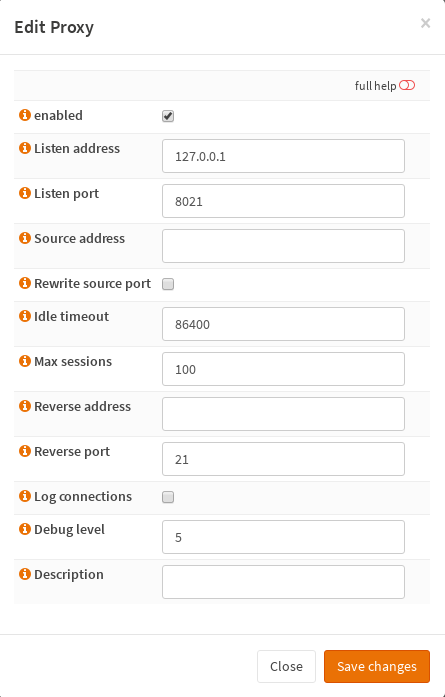
For now you can leave the defaults.
Clicking on Save changes creates a new FTP proxy server and starts it. Be patient, this takes a few seconds.
Now this proxy listens on 127.0.0.1 on port 8021 and you should see it as a new entry in the proxy server list.
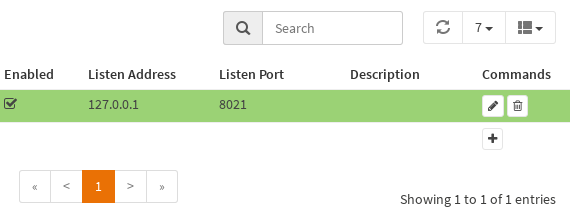
The green background indicates that the proxy is running. If the background appears yellow it is disabled and stopped.
Next we create rules to allow and redirect FTP from LAN interface to the proxy.
Go to Firewall->NAT->Port Forward and click on the Add Button.
Here we change following options:
Interface: LAN
Destination: any
Destination port range: FTP
Redirect target IP: 127.0.0.1
Redirect target port: (other) 8021
This will create a redirect rule for all FTP connections to the internet

and a rule to allow FTP connections to the proxy. (See Firewall->Rules->LAN)

Apply these changes and you can connect FTP server on the internet.
Reverse FTP Proxy
The reverse proxy enables access from internet to a local FTP server behind the firewall.
Clients connecting the firewall via FTP will be redirected to a local FTP proxy and then to the internal FTP server.

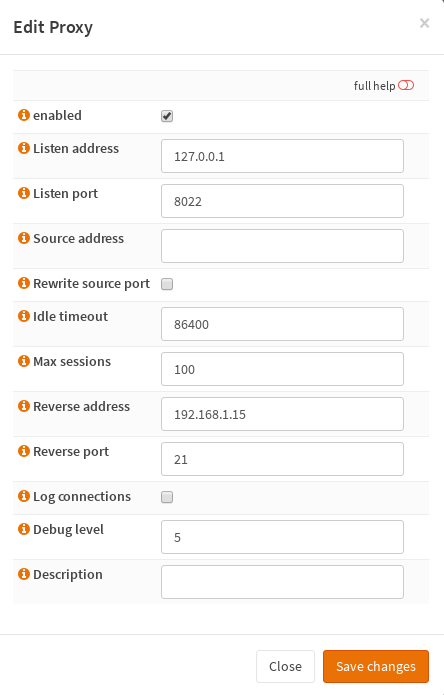
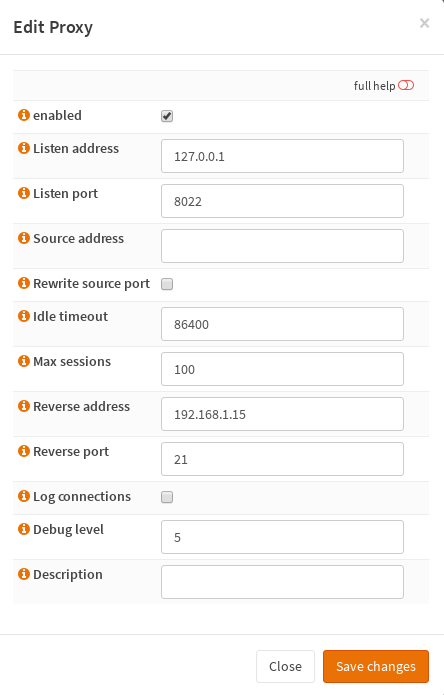
So let's create a new FTP proxy and configure the "Reverse address" to point to the internal FTP server at 192.168.1.15.
Here we need the rules to redirect the traffic from the WAN Interface to the proxy as well.
Go to Firewall->NAT->Port Forward and add a new rule:
Interface: WAN
Destination: WAN address
Destination port range: FTP
Redirect target IP: 127.0.0.1
Redirect target port: (other) 8022
And additionally to the auto generated rules we allow FTP access to the WAN interface.
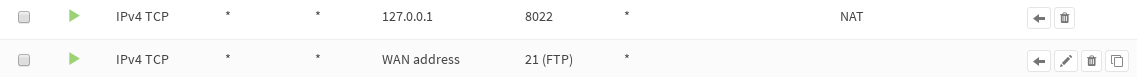
Apply the changes and the FTP server is accessible from the internet.
This how-to describes the steps to allow FTP traffic from your local network to the internet and from the internet to a FTP server protected by your OPNsense firewall.
Prerequisites
To allow FTP traffic we have to redirect all FTP connections to a local FTP proxy server which dynamically inserts and removes firewall rules according to the FTP port commands.
Additionally we need rules to allow traffic on the local interface to this proxy.
For the setup of the proxy we use the "Ftp Proxy" plugin. It was released with OPNsense 16.7.8.
Forward FTP Proxy
The forward proxy enables internal clients to connect to FTP servers on the internet.

To add a new FTP proxy server navigate to Services->FTP Proxy and click on the Add Button bottom right.
Now you see a dialog with the proxy settings.
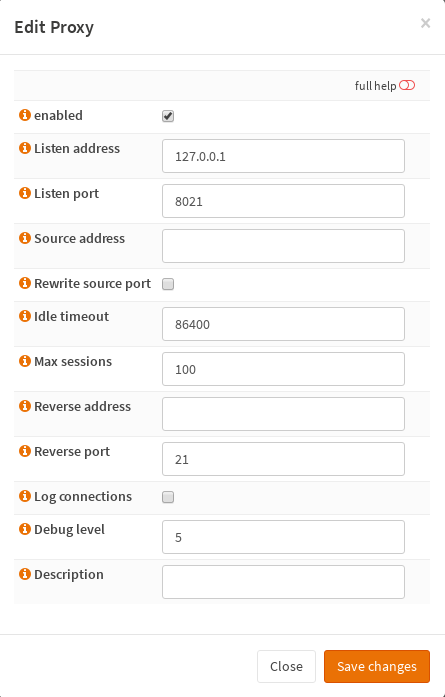
For now you can leave the defaults.
NOTE: If the outbound NAT address is different than the primary interface address you need to specify the NAT address as "Source Address".
This is probably the case in clustered setups with CARP.
Clicking on Save changes creates a new FTP proxy server and starts it. Be patient, this takes a few seconds.
Now this proxy listens on 127.0.0.1 on port 8021 and you should see it as a new entry in the proxy server list.
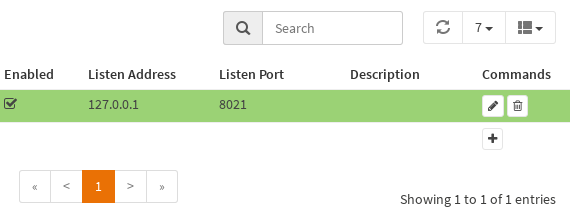
The green background indicates that the proxy is running. If the background appears yellow it is disabled and stopped.
Next we create rules to allow and redirect FTP from LAN interface to the proxy.
Go to Firewall->NAT->Port Forward and click on the Add Button.
Here we change following options:
Interface: LAN
Destination: any
Destination port range: FTP
Redirect target IP: 127.0.0.1
Redirect target port: (other) 8021
This will create a redirect rule for all FTP connections to the internet

and a rule to allow FTP connections to the proxy. (See Firewall->Rules->LAN)

Apply these changes and you can connect FTP server on the internet.
Reverse FTP Proxy
The reverse proxy enables access from internet to a local FTP server behind the firewall.
Clients connecting the firewall via FTP will be redirected to a local FTP proxy and then to the internal FTP server.

So let's create a new FTP proxy and configure the "Reverse address" to point to the internal FTP server at 192.168.1.15.
Here we need the rules to redirect the traffic from the WAN Interface to the proxy as well.
Go to Firewall->NAT->Port Forward and add a new rule:
Interface: WAN
Destination: WAN address
Destination port range: FTP
Redirect target IP: 127.0.0.1
Redirect target port: (other) 8022
And additionally to the auto generated rules we allow FTP access to the WAN interface.
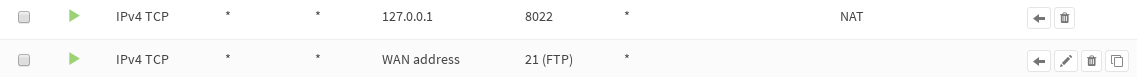
Apply the changes and the FTP server is accessible from the internet.




